A Few Tips and Tricks for Using 2nd Gen Cloud Functions
Table of Contents
- How to Handle Cloud Function Traffic Splitting
- Modify the Managed Traffic
- What Policy Permissions Are Required to Run gcloud functions deploy
Introduction
This post covers a few tips for using the 2nd generation of Google Cloud Functions, including traffic splitting between revisions and the required permissions for deploying functions.
How to Handle Cloud Function Traffic Splitting
From the 2nd generation of Cloud Functions, you can split the traffic between revisions or roll back the function to a previous version. Google announced this feature around August 9, 2022. Although I think AWS Lambda already had this feature a few years before that, it is still a good feature to have for serverless cloud functions.
The reason Cloud Functions can provide traffic splitting is that 2nd gen Cloud Functions use Cloud Run.

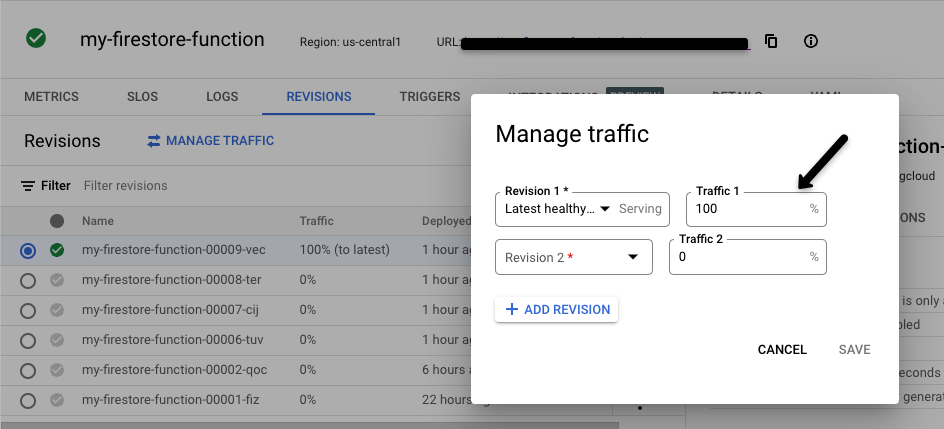
Modify the Managed Traffic
Once you click the link to go to Cloud Run from the Cloud Function page, then click REVISIONS. You can see all the versions of the Cloud Function that have been deployed. At this screen, you can either split the traffic 50% to the latest version and 50% to the previous version, or you can change the entire traffic to the previous version if there's any issue with the latest version.
What Policy Permissions Are Required to Run gcloud functions deploy
To run gcloud functions deploy, it seems like you need the Cloud Functions Admin role at least. I could not find documentation that specifies the exact permission for gcloud functions deploy, but I tested the following scenarios with a new user from the admin:
- Used the new email with the
Editorrole - Used the new email with the
Cloud Functions Developerrole
These two roles didn't work and threw errors when running the command gcloud functions deploy.
Conclusion
The 2nd generation of Cloud Functions brings useful features like traffic splitting through Cloud Run, allowing you to gradually roll out changes or quickly roll back if issues arise. When deploying, make sure the deploying user has at least the Cloud Functions Admin role to avoid permission errors.